Fraud Prevention: How to Confirm Addresses on Legal Documents

According to Visa, there is a 244% Y-o-Y rise in digital document forgery. Addresses are considered a low-risk form field, but they also hold an equal scope in forgeries like these. With a wrong or manipulated location, important documents and even payments can be misdirected from the actual recipients. That’s why address confirmations are equally as necessary as other metadata.
You can do that through a simple reverse lookup. A more in-depth investigation would involve a location-specific review on Mississippi.
Modern workflows value speed. In the process, they don’t mind ignoring small mistakes. Remote approvals have also peaked since COVID-19. This is encouraging to fraudsters.
They just have to prepare a clean and complete-looking document, and they’re good to go.
In this article, I’ll tell you how you can prevent address fraud even when the legal documents look completely clean.
KEY TAKEAWAYS
- Addresses are considered low-risk metadata, which is why they are increasingly prone to fraud.
- The risk level of a document can be categorized into 3 levels based on its importance.
- Adhere to a checklist for professional screening of documents for location errors.
Above the Fold: The 3-Level Address Confirmation Checklist
The intensity of an address-fraud prevention strategy can vary based on 3 levels of document importance, requiring different checklists of steps to follow.
Level 1: low-dollar, low-consequence documents
Level 1 is a fast and consistent low-risk workflow. The goal is to eliminate avoidable errors and create a clean audit trail without slowing the business down. This level covers routine documents where the consequence of an incorrect location is limited (e.g., non-sensitive correspondence, low-dollar agreements, or internal records).
Use a standardized checklist so staff don’t “wing it” under time pressure. Consistency matters more than perfect detective work at this level, and the documentation should be lightweight but complete.
Level 1 checklist (routine):
- Standardize the address format and correct obvious errors (street suffixes, directional, typos).
- Confirm city/state/ZIP alignment (deliverability check).
- Cross-check against one independent source already on file (prior invoice, prior signed contract, known customer record).
- Record who verified, when, and what sources were used.
Level 2: moderate dollar value or moderate fraud exposure
Level 2 is for workflows where spoofing is plausible and the downside is real – moderate dollar value, moderate fraud exposure, or moderate legal sensitivity. The upgrade here is simple: treat “the address looks normal” as insufficient, and add controls that answer, “Does this location exist as a deliverable point, and is there credible corroboration tying the party to it?”
At this level, address standardization helps, but teams should also use delivery point validation concepts where available. USPS-related coding and validation (e.g., CASS for standardization quality and DPV to confirm a deliverable point) are best treated as signals that a location exists and can accept mail, not proof that a person controls it (postalpro.usps.com). Level 2 also introduces a proof-of-address document with clear redaction rules so privacy risk does not balloon.
Level 2 checklist add-ons (enhanced):
- Delivery-point-level validation where available (especially for multi-unit addresses).
- Require one proof-of-address document (recent utility bill, bank/insurance statement) with redaction rules.
- Confirm whether the location is a commercial mail receiving agency or similar mailbox service when relevant (flag for escalation).
Level 3: high-dollar, litigation-sensitive, or wire-related matters
Level 3 is the company’s “assume the attack is in the change request” tier: high-dollar transactions, litigation-sensitive work, and anything wire-related. This is where teams should stop thinking in terms of “address accuracy” and start thinking in terms of control design: out-of-band confirmation, dual control, and strict change management.
Real-world fraud patterns frequently involve changed instructions delivered through persuasive email threads or polished PDFs. Best-practice guidance emphasizes verifying changes using known contact paths and requiring additional approvals for high-risk modifications. Level 3 is also where the company recommends treating location changes as materially riskier than initial entry.
Level 3 checklist add-ons (high assurance):
- Confirmation code sent to a validated postal address (when time allows) as an access check.
- Phone verification using a number from a trusted directory or pre-existing contact list (not from the email/PDF).
- Two-person review for any location change, payoff instruction change, or disbursement detail.
Define the Terms: Validation vs Verification vs Authorization
Many people get confused regarding what is covered under validation, verification, and authorization. That gets even more convoluted considering address fraud. Thus, it becomes important to distinguish between the three.
Address validation
Address validation answers a narrow question: Does this location exist in a recognized format and accept mail? It improves deliverability, reduces typos, and prevents internal mismatches that create false “exceptions.”
USPS-related frameworks like CASS are widely used to improve standardization and coding quality for address-matching accuracy (postalpro.usps.com). Useful – yes. Identity proof – no. Validation helps ensure the string represents a mailable location, but it does not establish who lives there, who controls it, or who should receive sensitive notices.
Address verification
Address verification is about the relationship between a party and the location. It requires corroboration (independent sources) and, for higher-risk cases, access checks (e.g., a mailed confirmation code).
Proof of address is best understood as a probability tool. A utility bill can be legitimate and still be unrelated to the signer; a government ID can be outdated; a bank statement can be edited. Verification is a layered process: multiple signals, weighed by risk, with documented exceptions.
Authorization
Authorization is the question legal operations often miss: even if the location is real and the party is connected to it, is the signer allowed to bind the entity in this context?
For businesses, address confirmation should pair with authority checks. For example, officer/agent authority and awareness of registered agent vs business location vs mailing address. Formal requirements vary by jurisdiction and document type; counsel should confirm what “good” looks like for the specific filing or transaction.
The Core Workflow Professionals Use: Standardize → Validate → Corroborate → Confirm → Document
Let me list down the steps of a professional workflow for address confirmation to prevent any related fraud.
Step 1: Standardize the address and capture it in structured fields
Clean data prevents downstream mismatches and makes cross-checking possible. The company recommends capturing addresses in structured fields, not a single free-text line. That includes a dedicated field for unit/suite and a policy for abbreviations and directional prefixes.
Standardization is also where many “false red flags” disappear: missing unit numbers, swapped ZIP digits, and inconsistent state abbreviations. Standardized coding programs exist to improve location-matching accuracy and consistency across systems (postalpro.usps.com).
Step 2: Validate deliverability
Deliverability validation checks that the address is a real delivery point, not just a plausible-looking string. Conceptually, DPV answers, “Is this a deliverable point?” – especially important for multi-unit buildings where a missing apartment number can turn a real building into an undeliverable destination (pe.usps.com).
Teams should also watch for “range-based” false positives: a location that fits a street range but doesn’t correspond to an actual mailbox. Validation helps reduce operational waste (returned mail, failed deliveries, broken notices), but it should not be confused with identity verification.
Step 3: Corroborate using independent sources
Two independent sources typically outperform one “strong-looking” document. The objective is not to collect a stack of paperwork; it is to select a few high-signal sources that are difficult to fake and relevant to the risk.
Ranked corroboration sources (and what each proves):
- Government-issued ID address: ties the person to a location historically; helpful, but often outdated and not sufficient alone.
- Recent utility bill or bank/insurance statement: shows ongoing activity linked to the address; requires strict redaction guidance.
- Property tax record/assessor record (ownership-linked cases): ties the location to ownership or assessed responsibility; strong for property scenarios, weaker for renters.
- Prior executed agreement on file: shows continuity with earlier verified work; strong if the prior file was vetted.
- Confirmed postal delivery record (where permissible/available): supports deliverability and potential access patterns; treat as a supporting signal, not a standalone proof.
A practical rule the company uses: if two independent sources disagree on unit number, city/ZIP, or the party name, escalate rather than “averaging” the truth.
Step 4: Confirm access using a mailed confirmation code for higher-risk cases
When time allows, a mailed confirmation code is a strong control because it verifies access to the address, not just formatting. This aligns with modern identity proofing patterns that use confirmation codes delivered through a validated channel as an access check.
It is not instantaneous, and it does not solve every scenario. But for high-dollar or litigation-sensitive matters, it can be the difference between “the location looked fine” and “the party demonstrated control of mail delivered there.”
Step 5: Document the decision and retain only what is needed
Good documentation is concise, consistent, and privacy-minimizing. The company recommends a simple structure: who/what/when/why, plus the verification level and sources used.
Retention should follow a minimization principle: store only what is required for auditability and dispute defense, and delete the rest on schedule. This reduces both breach impact and internal misuse risk.
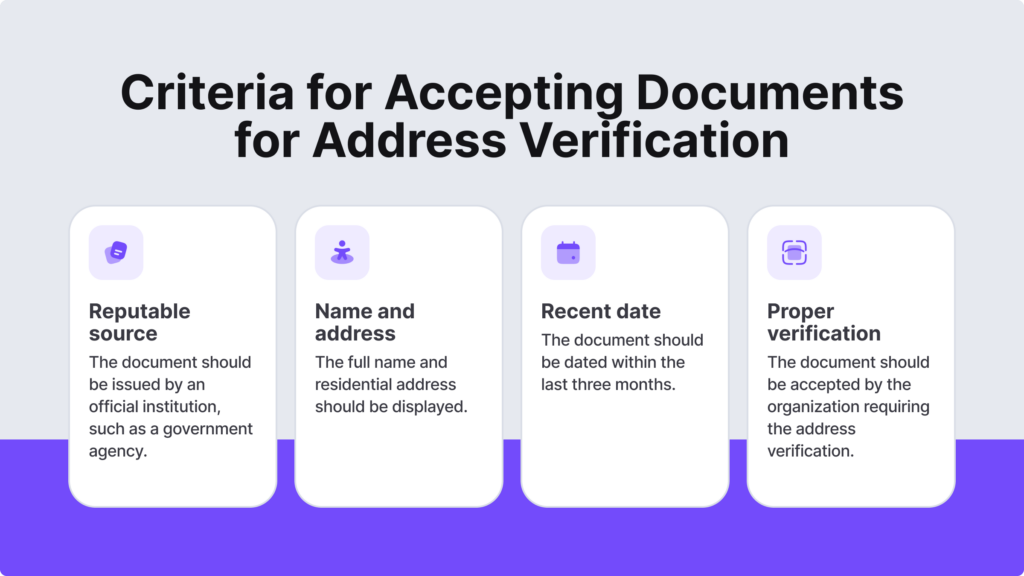
The following infographic lists the criteria for accepting legal documents for address verification:
Evidence Tiers: What to Accept, What to Flag, What to Reject
The address evidence can be strong, medium, or even high-risk.
Strong evidence
Strong evidence is reliable enough to carry weight without creating unnecessary friction. The company generally prefers fresh evidence (typically within the last 60–90 days) that is clearly attributable and difficult to edit without leaving traces.
Examples of strong evidence:
- Bank or insurance statements with consistent formatting and clear issuer identity
- Utility bills from recognized providers
- Property tax/assessor records for ownership-linked workflows
- Prior executed agreements already in the file (when the prior verification is trusted)
Name matching should be policy-driven: allow minor variations (middle initials, hyphenation, common abbreviations) but require escalation for materially different names.
Medium evidence
Medium evidence is often legitimate but easy to misinterpret or easy to forge. It can support a decision, but it should not stand alone in moderate-to-high risk cases.
Examples:
- Screenshots of “account pages.”
- Emailed PDFs without provenance.
- Editable documents (word-processed letters, unverifiable templates).
High-risk evidence
High-risk evidence is less about the document type and more about patterns that repeatedly show up in fraud attempts:
- Last-minute address changes.
- Mismatched unit numbers or missing apartment/suite.
- “Care of” names that don’t match the party.
- Inconsistent ZIP/city pairings.
- Pressure tactics (“must be done today,” “can’t take calls,” “use this new location immediately”).
What to do next (escalation steps):
- Move the case to Level 3 controls (out-of-band verification + dual control).
- Require two independent corroborations plus an access check if feasible.
- Reject changes delivered only via email/PDF when funds, legal exposure, or deadlines are involved.
High-Risk Scenarios Where Address Confirmation Must Be Stricter
As described in the previous section, high-risk evidence requires higher levels of scrutiny around address confirmations.
Any transaction involving fund transfer or payout instructions
Wire fraud prevention starts with a mindset: changes are suspect. When payout instructions or addresses change late in the process, teams should require out-of-band verification and dual approval. Best practice is to call a known number from a trusted source – never the phone number listed in the suspicious message or PDF.
This is where “no changes via email alone” becomes a control, not a preference.
Real estate and title-adjacent document
These workflows are heavily targeted because they combine urgency, large dollar values, and multi-party coordination. Attempted wiring and payoff changes are common enough to be operationalized: ALTA reported that over 40% of title companies saw at least one such email per month in 2023 (alta.org).
The company’s recommendation is to embed verification into the process: train staff on the “change request” attack pattern, require out-of-band confirmation, and use Level 3 dual control for any location or instruction changes that touch disbursements.
Corporate documents and filings
Fraudsters exploit confusion between “business address,” “registered agent location,” and “mailing address,” especially when teams are moving quickly. The company also sees scams that impersonate agencies and solicit sensitive information.
The rule is simple: verify communications through official channels and avoid inbound links or QR codes in unsolicited messages (fincen.gov). Location confirmation should be paired with authority checks and counsel review where formal legal requirements apply.
Conclusion: The Company’s Address-Confirmation Standard
The address confirmation process should be kept intentionally simple:
- Match risk to evidence.
- Then follow a repeatable workflow—standardize, validate, corroborate, and confirm (when needed).
- Document with minimization.
This approach does not promise perfection, but it consistently reduces rework, disputes, and loss events while improving defensibility.
Organizations institutionalize these controls because fraud losses operate at scale, as reflected in 2024 reporting from the FTC and FBI IC3. Done well, disciplined verification becomes faster over time: fewer exceptions, fewer reversals, and fewer costly mistakes triggered by a “small” location field treated as clerical.
Ans: It’s a process that validates that the given location is real, genuine, and accurate.
Ans: Govt.-issued IDs, utility bills, bank documents, and rent agreements.
Ans: Implement a checklist in the fraud prevention workflow to screen documents for location errors.